一、为什么要有Ingress?
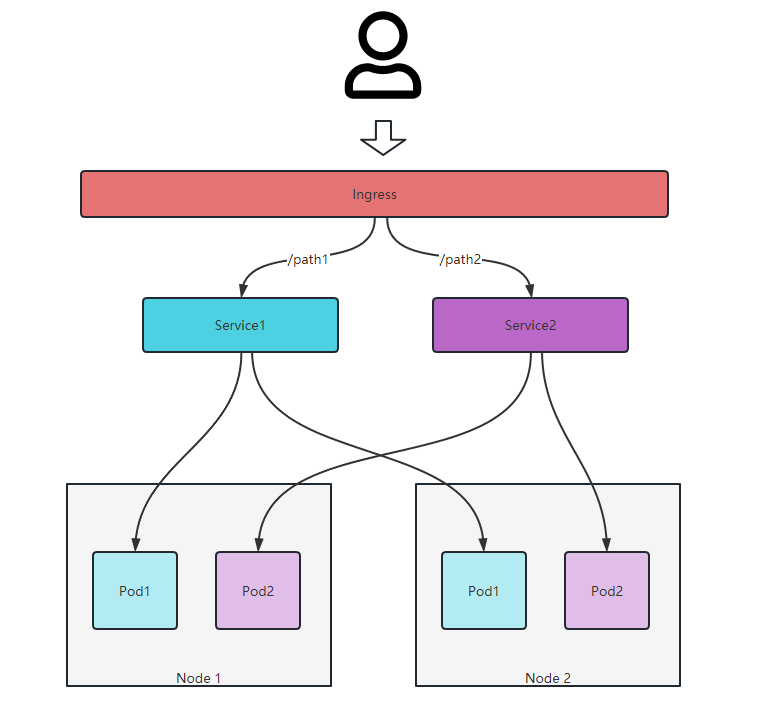
如果说Service类似于微服务架构中的注册中心,那么Ingress就类似于微服务架构中的网关,Ingress为kubernetes提供统一的入口,对外提供服务。我们知道NodePort Service也可以通过暴露端口的方式对外提供服务,但是当我们的Service非常多的时候,那么对于Service端口的管理将是一件比较困难的事情,而且默认情况下端口的范围也有只有30000-32767而已,很容易就耗完端口号。
因此,如果说Service是一组Pod的抽象的话,Ingress就是一组Service的抽象,使得调用者不用关注实际调用的是哪个Service,只需要关注具体服务接口即可。
二、Ingress简单使用
1、Ingress的组成
Ingress由Ingress控制器和Ingress配置文件组成,与作为kube-controller-manager可执行文件的一部分运行的其他类型控制器不同,Ingress控制器不是随集群自动启动的,需要先手动安装Ingress控制器,其中有kubernetes维护的Ingress控制器有:AWS、GCE和Nginx。此外,我们也可以选择第三方Ingress控制器(https://kubernetes.io/zh-cn/docs/concepts/services-networking/ingress-controllers/)。
ingress配置文件是一个API对象,通过yaml文件来配置,ingress对象的作用是定义请求如何转发到service的规则。
2、安装Ingress-NGINX
查看官方文档https://github.com/kubernetes/ingress-nginx/blob/main/README.md#readme,选择与当前环境的kubernetes版本匹配的Ingress-NGINX版本。
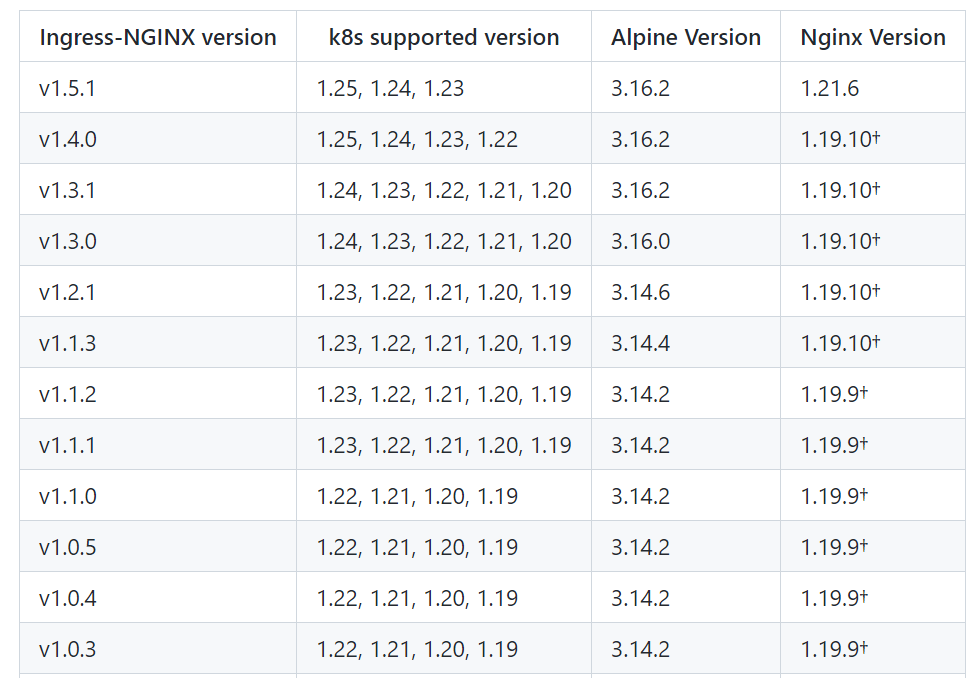
下载对应的Ingress-NGINX版本,由于我本地kubernetes版本为1.21,因此我这边选择Ingress-NGINX版本为1.3.1。查看官网介绍的安装文档https://kubernetes.github.io/ingress-nginx/deploy/ 选择适合自己的安装方式,我这边采用的是kubectl apply的方式进行安装。
(1)下载Ingress-NGINX配置文件
wget https://raw.githubusercontent.com/kubernetes/ingress-nginx/controller-v1.3.0/deploy/static/provider/cloud/deploy.yaml
由于各种原因,需要把镜像地址替换为国内的
sed -i s#registry.k8s.io/ingress-nginx/controller:v1.3.0@sha256:d1707ca76d3b044ab8a28277a2466a02100ee9f58a86af1535a3edf9323ea1b5#registry.cn-hangzhou.aliyuncs.com/google_containers/nginx-ingress-controller:v1.3.0#g deploy.yaml
sed -i s#registry.k8s.io/ingress-nginx/kube-webhook-certgen:v1.1.1@sha256:64d8c73dca984af206adf9d6d7e46aa550362b1d7a01f3a0a91b20cc67868660#registry.cn-hangzhou.aliyuncs.com/google_containers/kube-webhook-certgen:v1.1.1#g deploy.yaml
(2)修改配置文件
... ...
#kind: Deployment
kind: DaemonSet
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
app.kubernetes.io/part-of: ingress-nginx
app.kubernetes.io/version: 1.3.1
name: ingress-nginx-controller
namespace: ingress-nginx
spec:
minReadySeconds: 0
revisionHistoryLimit: 10
selector:
matchLabels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
template:
metadata:
labels:
app.kubernetes.io/component: controller
app.kubernetes.io/instance: ingress-nginx
app.kubernetes.io/name: ingress-nginx
spec:
hostNetwork: true # 这里加一句
containers:
- args:
... ...
dnsPolicy: ClusterFirst
nodeSelector:
kubernetes.io/os: linux
ingress: "true" # 这里加一句
serviceAccountName: ingress-nginx
... ...
说明:
a) 【DaemonSet】:让Ingress-NGINX部署到我们指定的node节点上,可控性更强。
b) 【ingress: “true”】 :增加ingress=true标签,用于给某些node节点打上标签,方便Ingress-NGINX安装。
c)【hostNetwork: true】 : 直接暴露宿主机的网络端口,而不再经过一层映射,效率更高。
(3)给node节点打上标签ingress=true
kubectl label nodes k8s-master1 ingress=true
注:删除标签kubectl label nodes k8s-master1 ingress- , 查看标签kubectl label nodes k8s-master1 --show-labels
[root@k8s-master1 ingress]# kubectl label nodes k8s-node1 ingress=true
node/k8s-node1 labeled
[root@k8s-master1 ingress]# kubectl get nodes --show-labels
NAME STATUS ROLES AGE VERSION LABELS
k8s-master1 Ready <none> 9d v1.21.0 beta.kubernetes.io/arch=amd64,beta.kubernetes.io/os=linux,kubernetes.io/arch=amd64,kubernetes.io/hostname=k8s-master1,kubernetes.io/os=linux,node.kubernetes.io/node=
k8s-node1 Ready <none> 9d v1.21.0 beta.kubernetes.io/arch=amd64,beta.kubernetes.io/os=linux,ds=true,ingress=true,kubernetes.io/arch=amd64,kubernetes.io/hostname=k8s-node1,kubernetes.io/os=linux,node.kubernetes.io/node=
[root@k8s-master1 ingress]#
(4)执行Ingress-NGINX安装
kubectl apply -f deploy.yaml
[root@k8s-master1 ingress]# kubectl apply -f deploy.yaml
namespace/ingress-nginx created
serviceaccount/ingress-nginx created
serviceaccount/ingress-nginx-admission created
role.rbac.authorization.k8s.io/ingress-nginx created
role.rbac.authorization.k8s.io/ingress-nginx-admission created
clusterrole.rbac.authorization.k8s.io/ingress-nginx created
clusterrole.rbac.authorization.k8s.io/ingress-nginx-admission created
rolebinding.rbac.authorization.k8s.io/ingress-nginx created
rolebinding.rbac.authorization.k8s.io/ingress-nginx-admission created
clusterrolebinding.rbac.authorization.k8s.io/ingress-nginx created
clusterrolebinding.rbac.authorization.k8s.io/ingress-nginx-admission created
configmap/ingress-nginx-controller created
service/ingress-nginx-controller created
service/ingress-nginx-controller-admission created
daemonset.apps/ingress-nginx-controller created
job.batch/ingress-nginx-admission-create created
job.batch/ingress-nginx-admission-patch created
ingressclass.networking.k8s.io/nginx created
validatingwebhookconfiguration.admissionregistration.k8s.io/ingress-nginx-admission created
[root@k8s-master1 ingress]#
root@k8s-master1 ingress]# kubectl get pods -n ingress-nginx -o wide
NAME READY STATUS RESTARTS AGE IP NODE NOMINATED NODE READINESS GATES
ingress-nginx-admission-create-gj84p 0/1 Completed 0 15m 172.16.159.144 k8s-master1 <none> <none>
ingress-nginx-admission-patch-2cprw 0/1 Completed 1 15m 172.16.159.145 k8s-master1 <none> <none>
ingress-nginx-controller-xxjd2 1/1 Running 0 68s 192.168.253.110 k8s-master1 <none> <none>
3、配置ingress
当前kubernetes环境已经存在service
[root@k8s-master1 ~]# kubectl get service
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
kubernetes ClusterIP 10.96.0.1 <none> 443/TCP 9d
nginx-external-service ClusterIP 10.99.156.71 <none> 80/TCP 22h
nginx-service ClusterIP 10.100.208.173 <none> 80/TCP 26h
我们拿nginx-service进行测试,下面定义一个ingress。
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: ingress-nginx
spec:
ingressClassName: nginx
rules:
- host: ingress.greaterway.cn
http:
paths:
- path: /
pathType: Prefix
backend:
service:
name: nginx-service
port:
number: 80
执行创建并查看
[root@k8s-master1 ingress]# kubectl apply -f 01-create-ingress.yml
ingress.networking.k8s.io/ingress-nginx created
[root@k8s-master1 ingress]# kubectl get ingress
NAME CLASS HOSTS ADDRESS PORTS AGE
ingress-nginx nginx ingress.greaterway.cn 80 13s
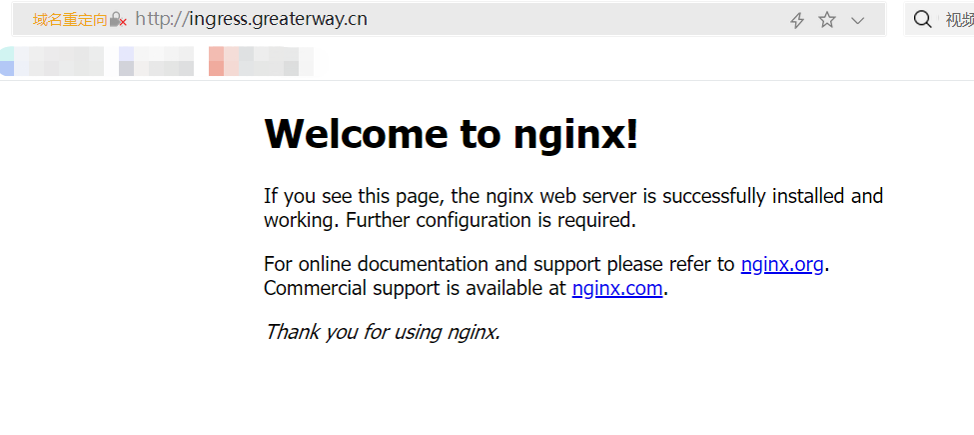
4、测试
在本地机器上添加hosts配置
192.168.253.110 ingress.greaterway.cn
在浏览器输出http://ingress.greaterway.cn/